Windows XP And Vista On The LAN Together
File and Printer Sharing in Windows Vista is not extremely different from File and Printer Sharing in Windows XP. There are new features, and wizard procedures, that work on top of Windows XP features and procedures. If you have a working network, with one or more computers that use Windows Networking, you probably know enough to get started.
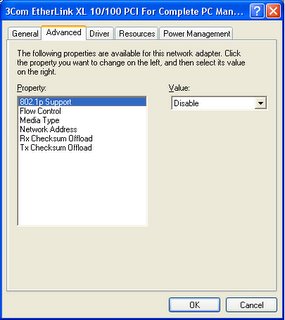
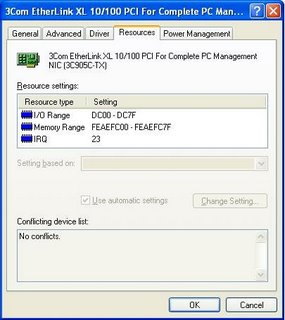
There will be challenges though. One predictable challenge is the availability (or lack of availability) of drivers for devices that are operating system sensitive, like network adapters. This has inspired various attitudes, even rants, among the user community.
Computers running Windows Vista use the same layered network as previous versions of Windows, so start by reviewing the principles of layered network design and installation, and of layered network problem solving. And review various issues that affected Windows Networking on computers running Windows XP.
>> Top
System Updates Issues
With Windows Vista, as with Windows XP, Microsoft will issue periodic (and monthly) updates. Most updates are for security issues, and others for operability and / or stability. All updates are necessary, if recommended for your edition of Vista, and some may have a direct effect on your problem.
As an interim measure, possibly before an actual Service Pack, Microsoft has started issuing compatibility, performance, and reliability fixes, covering a variety of issues with Vista.
>> Top
Connectivity Issues
By default, computers running Vista will set the Broadcast flag, in the DHCP Discover packets, On. If your DHCP server (NAT router, or non-Microsoft dedicated server) doesn't support DHCP Broadcast, you'll have various problems - your computer may never get an IP address, or your IP connectivity may come and go unpredictably. To make your Vista computer compatible with Windows XP, (KB928233): turn the DHCP Broadcast flag Off. Besides the DHCP Broadcast difference, be aware of an interesting (KB931550): timing difference between the Windows Vista and XP DHCP clients.
One of the most interesting features in Vista (my opinion anyway) is the ability to dynamically determine Receive Window size for each individual Internet connection. Users of high speed broadband connections will be especially interested in this. Unfortunately, it appears that RWin AutoTuning may be a bit problematic. This setting has been observed to affect both LAN and WAN connectivity, and can cause instability, or lack of connectivity.
On laptop computers, and other computers with multiple network adapters, you'll see an inaccurate / inconsistent network status indicator, when the computer is first started.
Like every newer version of Windows, Windows Vista will use more resources on the host computer, and on any peripherally connected computers and routers. If your peripheral network equipment like routers are becoming aged, you'll be advised to upgrade or replace whatever you can.
The IPX/SPX Protocol is not provided in Windows Vista, though Novell does now provide a Netware client for Vista. NetBEUI, on the other hand, is now a part of history.
>> Top
Visibility Issues
One of the new features of Windows Vista is the Network Map, which runs at the Link Layer of the OSI Network Model, and offers functions similar to The Dude. The Network Map uses a discovery protocol called Link-Layer Topology Discovery (LLTD), which is not a normal part of Windows XP.
To be able to see a Windows XP server from a Vista client, using the Vista Network Map, you need to install (KB922120): the LLTD Responder on any Windows XP computers. The LLTD Responder isn't available for Windows 2000, so you won't be able to see a Windows 2000 server from a Vista client, using the Vista Network Map.
Even if you can't see a Windows XP or 2000 computer in the Network Map, though, you'll still be able to see it in Network Neighborhood / My Network Places, aka the Network window (Start - Network) in Windows Vista. And even if you can see a computer in the Network Map, you may still have to work on name resolution, or on sharing permissions, if you are going to actually access its resources.
The simplest visibility will be enjoyed with all computers in the same workgroup. By default, Windows Vista uses "Workgroup", while Windows XP uses "MSHome". If you leave workgroup names at default, the other computers will be visible in the Network (My Network Places aka Network Neighbourhood) wizard, but they won't be seen immediately, when you open the wizard. You may have to look under Entire Network - Microsoft Windows Network, for the different workgroups used by each set of computers. And with having multiple browse domains (workgroups), your browser infrastructure will be slightly more complex.
>> Top
Using A Windows Vista Client
Under Windows Vista, the personal storage (personal profile and other files and folders) container has been changed, from "C:\Documents and Settings", to "C:\Users". The folder "C:\Documents And Settings" will continue to exist, for backward compatibility, only as a junction point. On a mixed LAN, I would very carefully test sharing of either "C:\Documents and Settings" (with a Windows Vista client), or "C:\Users" (with a Windows XP client), before committing myself.
>> Top
Setting Up A Windows Vista Server
If you're adding a computer running Windows Vista to your network, you have to set it up as a server, so you can access it from your other computers. You do this using the Network and Sharing Center wizard, accessed by Start - right-click on Network, and select Properties. This is equivalent to running the Network Setup Wizard, in Windows XP.
- Set the Network Location Type to "Private". This requires that your computers are secure, behind a perimeter firewall or a NAT router, and opens the standard Vista personal firewall to allow Server Message Blocks (SMBs) to pass between the computers. If your computer is directly connected to your Internet service, either get a NAT router, or leave the Network Location Type set to Public (which will prevent you from networking this computer).
- Having set the NLT to "Private", you must now designate which services you wish for your server to provide or use. You should verify each setting before continuing, and change it if necessary.
- File sharing.
- Public folder sharing.
- Printer sharing.
- Password Protected Sharing (PPS) affects the above 3 services. Disabling PPS is the equivalent of enabling Simple File Sharing, in Windows XP.
- Setup shared folders and printers. If you enabled PPS, you should setup access for individual users. If you disabled PPS, you setup access for "Guest" or "Everyone". Since Vista security is "deny by default (permit by demand)", "Everyone" doesn't automatically have access to newly created shares. Check the Security tab, for each share created, if you disable PPS.
- Whether you setup the server with PPS Enabled (aka Advanced File Sharing, in Windows XP), or PPS Disabled, make sure that the account used for sharing is activated for network use.
- If you Enable PPS, you can use either the Guest account, or a non-Guest account of your choice, but the chosen account has to be activated for network use.
- If you Disable PPS, then the Guest account must be activated for network use. By default, Guest is disabled. If your server provides network access through the Guest account, be aware of its limitations.
- Whether you use Guest, or a non-Guest account for access, the account used has to be added, explicitly, under Security, and under Sharing.
- On a server running Windows Vista, the Administrative (Hidden) volume share of "C$ ("D$", etc) isn't defined, by default.
For an overview of the above, see Microsoft: File and Printer Sharing in Windows Vista
>> Top
Setting Up A Windows XP Server
If you have just one computer besides your computer running Vista, you may have to setup your first computer as a server too. On a computer running Windows XP, run the Network Setup Wizard. For a server connected behind a NAT router, select
This computer connects to the Internet through another computer on my network or through a residential gateway.Running the NSW, and making that selection, is similar to setting the Vista NLT to "Private".
>> Top
Common Issues
Other than the network setup wizards used, Vista will be pretty similar to XP. You'll have the same challenges with Windows Networking.
- Make sure that NetBT is Enabled consistently.
- Make sure that all personal firewalls are properly setup.
- Make sure that name resolution is consistently setup.
- If you intend to use the Network window (pka "Network Neighbourhood" / "My Network Places"), instead of or in addition to, the Vista Network Map, to find the other computers, setup a reliable browser infrastructure.
- Remember to always check for well known error messages, when diagnosing problems.
>> Top
Editions Of Windows Vista and XP
There are 5 editions of Windows XP, which are basically 2 variants - Home and Pro.
- XP Home is the equivalent of Vista Basic Home, with PPS permanently disabled.
- XP Pro can use Advanced File Sharing (similar to PPS Enabled), or Simple File Sharing (similar to PPS Disabled).
- The other 3 editions - Media Center, Tablet, and Pro x64 - are all variants of XP Pro, in terms of file sharing functionality.
- With XP Pro, and with all editions of Vista, you can have Guest or non-Guest authentication. Note the limitations of Guest authentication carefully, some limitations aren't as obvious as they should be.
- Whether you use the Guest account, or a non-Guest account, for authentication, make sure that the account used is properly prepared for network access.
There are also 5 well known editions of Windows Vista, plus several obscure ones which we probably won't encounter. The different editions of Windows Vista are completely different from Windows XP, in feature set differentation.
>> Top
Windows Vista and Older / Other Operating Systems
If you also have one or more computers running Windows 9x (95, 98, ME), you'll need to be aware of a significant difference between Windows XP and Vista, in Microsoft Windows And Authentication Protocols. But focus your mind on the future - Windows 95 / 98 / ME have a limited life span.
This will be a problem, too, if you have a Network Attached Storage (NAS) device. Many NAS devices, with unknown authentication abilities, will be a similar challenge. Some NAS devices will also try to act as a master browser on your network, and will cause master browser conflicts, and unreliable displays in Network (aka My Network Places).
>> Top
Windows Vista and Printers
If you are setting up your mixed LAN specifically to share a printer, note the additional challenges involved in sharing printers. Get file sharing working, first, then concentrate on getting working printer drivers that support Windows Vista. On a mixed network, the printer will have to support both Windows Vista, and Windows XP. And drivers for the client will probably differ from drivers for the server.
If you're having problems with printing from a computer running Vista, and the printer is shared by another computer, read Network Printing From A Windows Vista Computer.
>> Top
Windows Vista and Security
Depending upon what personal firewall you are using on your Windows Vista computer, you may have to set the firewall manually. It appears that Windows OneCare does not setup seamlessly, as Windows Firewall does, when you set the Network Location Type. And a recent change (September 2007) in Internet Explorer appears to affect Windows Networking access between computers.
>> Top
More References
For the above issues, and more, see
- File Sharing: PChuck's Network: File Sharing Under Windows XP / Vista
- General Issues: PChuck's Network: Windows Vista Issues
- Windows Networking: PChuck's Network: Irregularities In Workgroup Visibility
>> Top